What is Social Engineering? (The Art of Human Hacking)
What is a hacker’s single most effective tool? It’s not a complex piece of code or a supercomputer. It’s the…
What is a hacker’s single most effective tool? It’s not a complex piece of code or a supercomputer. It’s the…
In our digital lives, we are protected by a series of secret keys: our passwords. They guard everything from our…
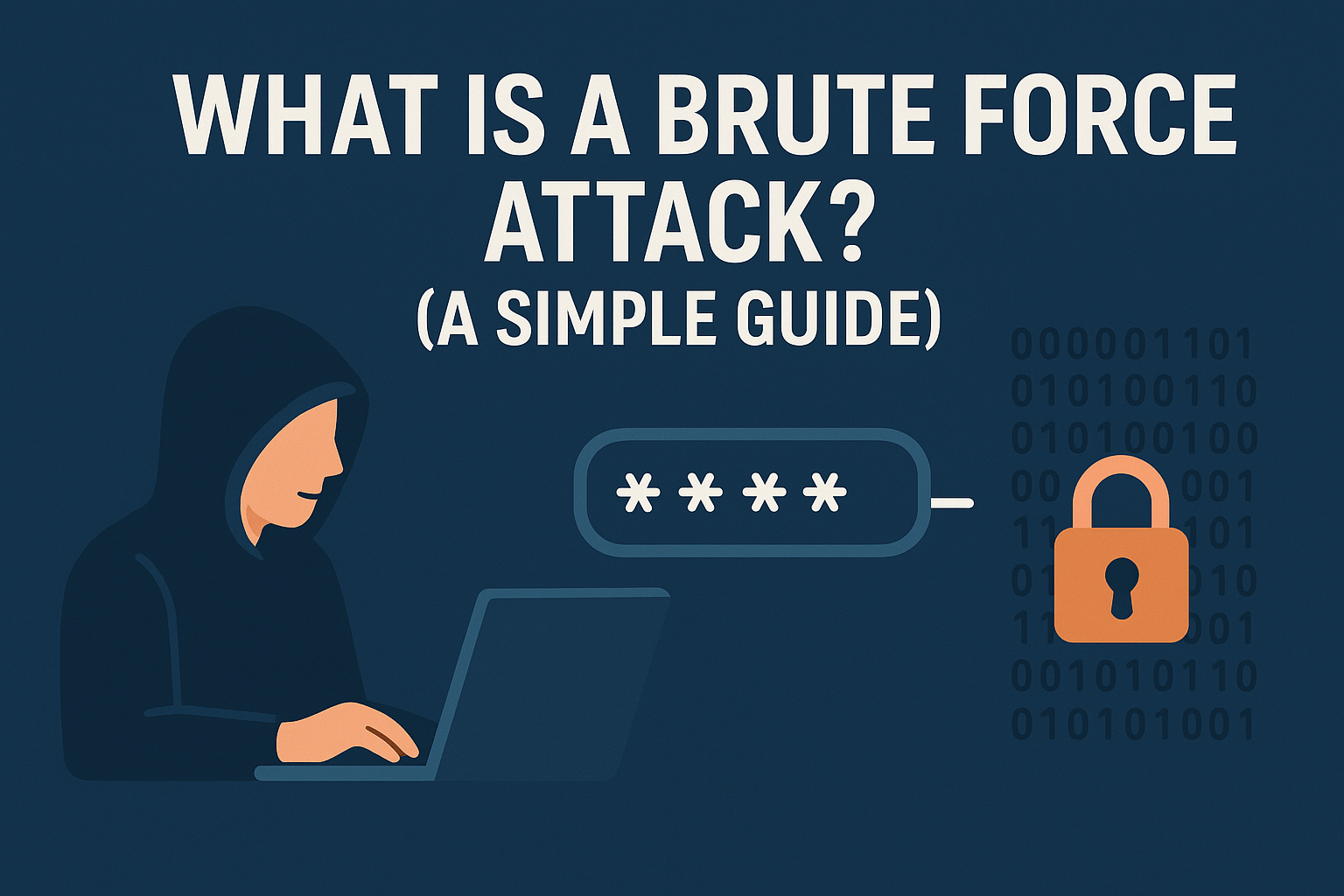
Imagine a thief trying to open a bicycle lock. Instead of skillfully picking it, they simply sit down and try…
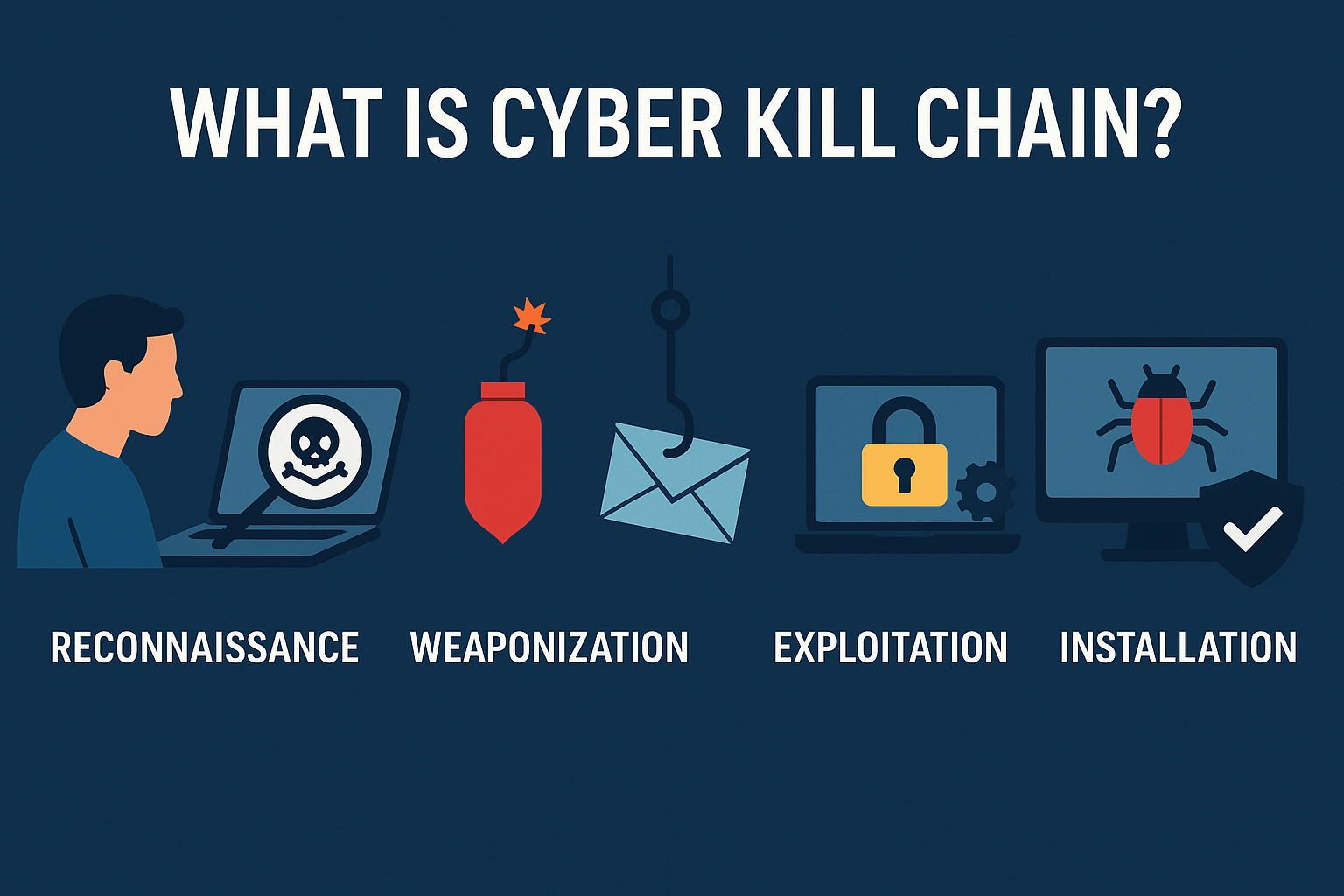
A successful cyberattack isn’t a single event; it’s a carefully planned campaign with multiple, distinct stages. To defend against an…

In our previous guides, we’ve talked about the dangers of phishing attacks and the importance of creating strong passwords. But…
In our last guide, we explored the dangerous world of malware, from viruses and worms to ransomware. The #1 tool…
You’ve probably heard someone say, “I think my computer has a virus!” While they might be right, “virus” is just…

In our last guide, What is Phishing?, we explained how hackers use deceptive messages to trick you into giving up…

You’ve likely heard the term “phishing” before, but what does it actually mean? It’s more than just a spam email;…

Who Are Black Hat Hackers? A Look at the Bad Guys of Cybersecurity In our previous posts, we’ve explored the…