What is Social Engineering? (The Art of Human Hacking)
What is a hacker’s single most effective tool? It’s not a complex piece of code or a supercomputer. It’s the human mind. The art of exploiting human psychology to bypass security is called Social Engineering, and it’s often the first step in a major cyberattack. In our previous lessons, we’ve talked about what malware is […]
How to Use VirusTotal: A Beginner’s Guide to Checking Files & Links
You’ve just received a strange email with an attachment you weren’t expecting. You know from our guide to spotting phishing attacks that you should never open it blindly. So, what’s the next step? Before you delete it, you can investigate it like a security professional. The first and most important tool for this job is […]
What Does a Firewall Protect Against? (A Simple Guide)
You’ve probably heard that you need a firewall to be safe online, but what does a firewall actually do? Think of a firewall as the security guard standing at the gate of your computer network. Its only job is to inspect every piece of data trying to get in or out and decide if it’s […]
How to Create Strong Passwords (and Actually Remember Them)
In our digital lives, we are protected by a series of secret keys: our passwords. They guard everything from our private emails to our financial information. Yet, the most common mistake people make online is using weak, predictable, and reused passwords. Hackers love weak passwords because they are easy to guess with automated software. But […]
What is a Brute Force Attack? (A Simple Explanation & How to Stop It)
Imagine a thief trying to open a bicycle lock. Instead of skillfully picking it, they simply sit down and try every single possible combination, starting from 0000, then 0001, 0002, and so on. Given enough time, they are guaranteed to find the right code. This is exactly how a brute force attack works in the […]
Networking Basics for Beginners: A Simple Guide to IP Addresses & Ports
Before you can understand how a cyberattack works, you first need to understand the roads it travels on. Every action online, from sending an email to visiting a website, happens over a computer network. Think of it as the invisible nervous system of the digital world. This guide won’t be a complex technical manual. Instead, […]
What is the Cyber Kill Chain?
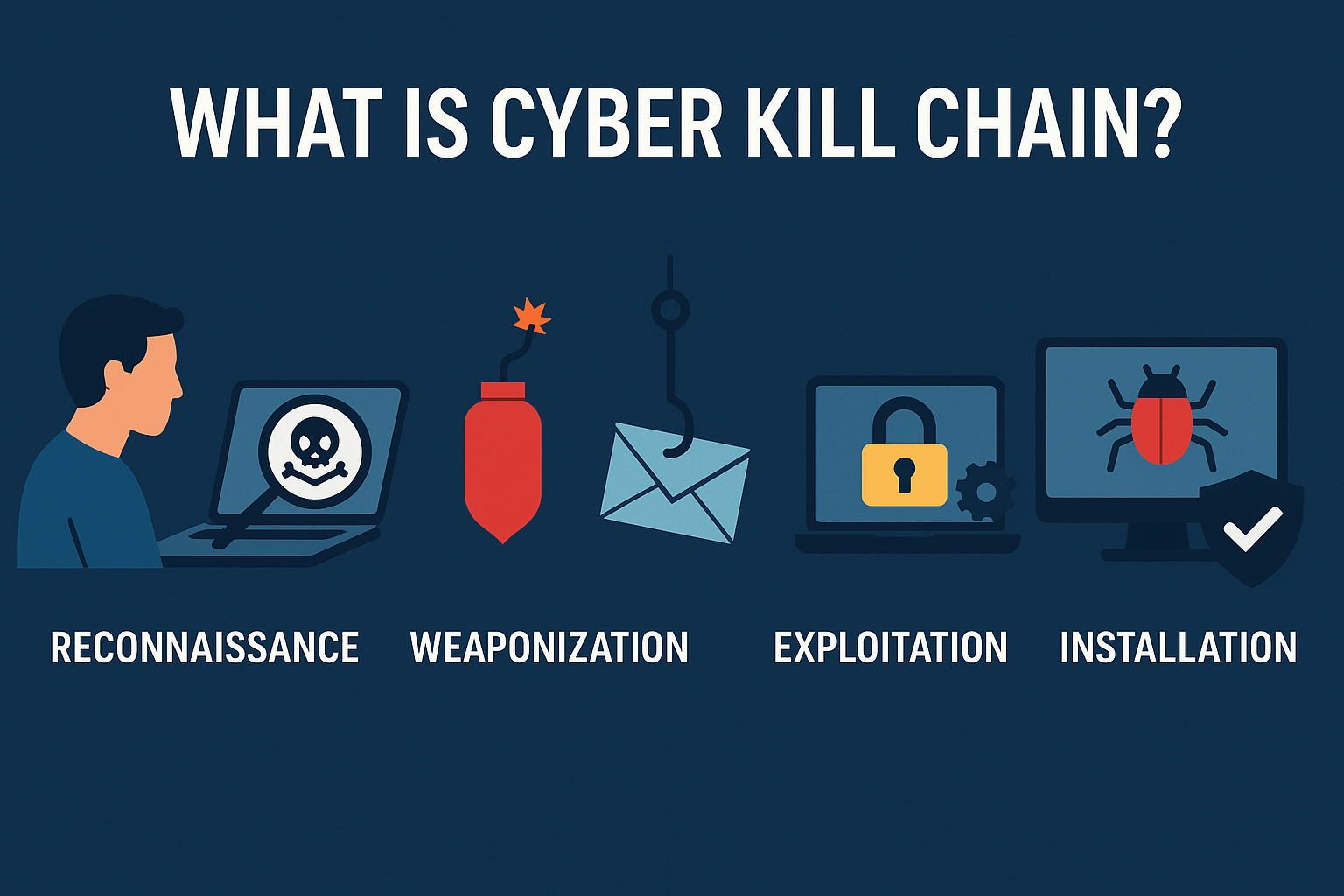
A successful cyberattack isn’t a single event; it’s a carefully planned campaign with multiple, distinct stages. To defend against an enemy, you must first understand how they think and operate. This is where the Cyber Kill Chain comes in. The Cyber Kill Chain is a framework originally created by defense company Lockheed Martin that outlines […]
What is a VPN and Why Do You Need One?
Have you ever connected to the free Wi-Fi at a coffee shop, airport, or hotel? It’s convenient, but it can also be incredibly risky. On a public network, your online activity can be easily monitored by hackers looking to steal your passwords and personal information. This is where a VPN comes in. It’s one of […]
What is 2FA? A Simple Guide to Securing Your Accounts
In our previous guides, we’ve talked about the dangers of phishing attacks and the importance of creating strong passwords. But what happens if a criminal manages to steal your password anyway? In today’s world of massive data breaches, this is a constant risk. This is where your most powerful defense comes into play: Two-Factor Authentication […]
What is Antivirus Software? A Simple Guide to How It Works
In our last guide, we explored the dangerous world of malware, from viruses and worms to ransomware. The #1 tool in our defensive arsenal against these threats is antivirus software. But what is it, and how does it actually protect your devices? Many people think of it as a simple “virus scanner,” but modern antivirus […]
